Services
Below is an overview of services we bring to your organization
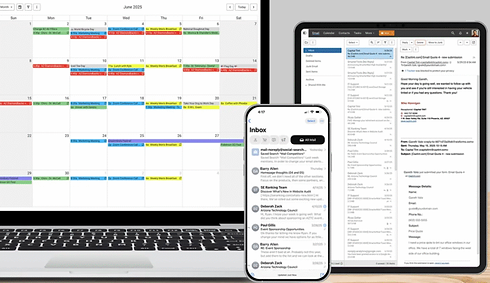
Secure Email
Access Secure Email with Large File Sending, Telehealth, Chat, Calendar, Contacts, Tasks, and Notes with built-in sharing capabilities. Enjoy the convenience of drag-and-drop functionality and right-click menus for a seamless, desktop-like experience right in your browser.
EChat
eChat is our secure internal messaging service with real-time texting, video, audio, and group chat. Designed for seamless communication between team members. Access it directly through Webmail or use any secure chat desktop app on your PC or Mac.
Secure File Link™
Easily share large files up to 2GB from our secure cloud with built-in password protection and optional expiration settings. Just upload your file through Webmail and send the recipient a secure download link. No more file size limits or email provider restrictions.
Telehealth
Our Webmail includes integrated, HIPAA-compliant video conferencing and screen sharing. No plugins, apps, or software to install. Host secure, private sessions with patients, team meetings, or collaborate with up to 9 participants, all directly within your web browser.
Hassle-Free Encrypted Email
No Gateways, Certificates, or Plug-ins. Send password-protected, encrypted messages effortlessly at no additional costs. Simply type “secure” in the subject line to encrypt your email. Recipients can reply securely, enabling true end-to-end encryption with ease.
Say Goodbye to Spam and Viruses
Our state-of-the-art anti-spam system blocks over 95% of unwanted messages. Easily block specific senders or whitelist trusted contacts to ensure important emails always get through. Our premium anti-virus engine updates hourly and scans every message to protect you from malware and infected attachments.
End-to-End Encryption: Complete Protection for PHI
End-to-end encryption secures data throughout its entire journey, from sender to recipient, making it one of the most effective methods for protecting sensitive information. As encrypted data moves across multiple servers, it remains protected against unauthorized access.
Encryption works by applying a complex algorithm that transforms readable data into an unreadable format, making it virtually impossible to trace back to an individual without the correct decryption key. This process not only strengthens compliance and simplifies audits but also empowers patients with greater control over their personal health information.